Smart toys are a new target for cybercriminals. Follow these tips to buy and configure them safely.

In Cybersecurity we can say that any device that can connect to the Internet is likely to be attacked. Therefore, smart toys should be treated like any connected device in terms of security settings. Both in the choosing and buying process as in its configuration once removed from the package.
With a few simple tips we will prevent our children’s data from being processed and used for advertising purposes. Or, worse still, being stolen by cyber attackers.
This is especially important when it comes to devices that store information about children. Data that can even be videos or photographs, as with some cameras and smart watches for children.
Before buying smart toys…
When we buy a toy we can recognize if it is a connected device, if it has a camera or microphone and uses the Internet, either because the toy has a WiFi connection or because it has a mobile application that connects to the Internet.
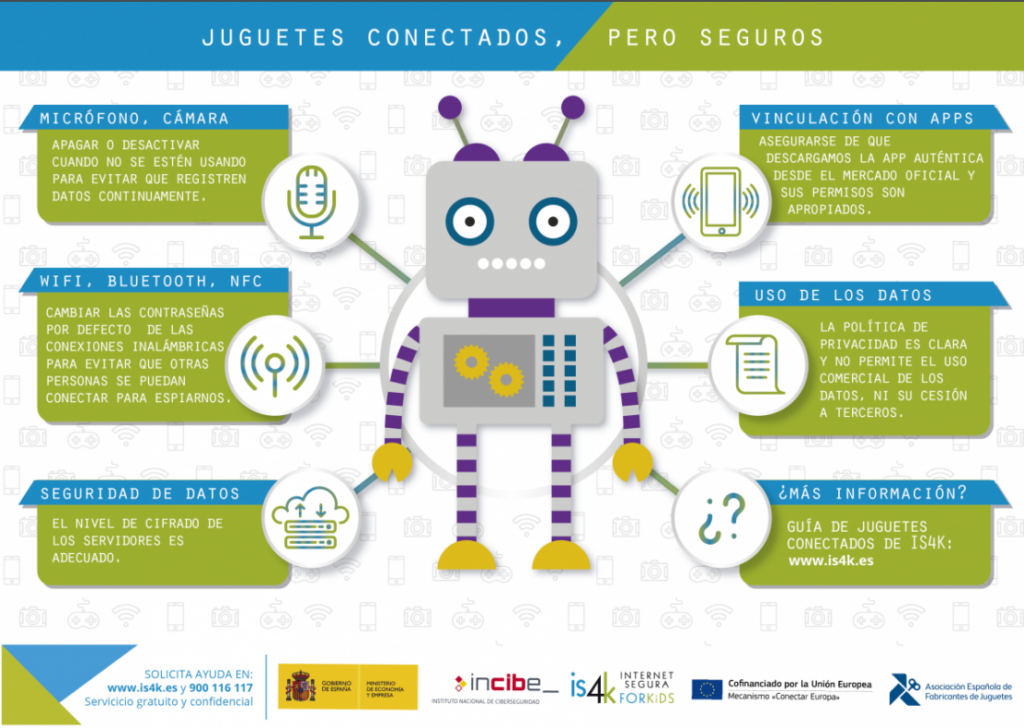
If the device has any of these characteristics we must perform a series of checks:
Check the Privacy Policy
The privacy policies of IoT (Internet of Things) devices should explain what data is collected and the purpose of collecting them. In this way, we can choose not to use the ‘smart’ features if we see that the toy aims to offer targeted advertising to the child or sell family personal data to third parties. Something that could also go against data protection laws.
Check if it requests registration on a web page or application
Some connected toys allow you to extend the playing experience by using the manufacturer’s website or an application. In this register the manufacturer may request personal data and other valuable information. It can also happen that this extension of the game is about cloud storage of the information collected (audios, photographs, videos, interaction data …).
In these cases, we must bear in mind that these services can be attacked by cybercriminals, as has happened with the smart toy company VTech, from which credentials, photographs and personal data of 5 million users were captured.
If we have to register in order to use the toy, we can take measures like these:
- Use invented data, as far as possible
- Do not use real photos that allow to identify your children.
- Consider using a specific email account for this type of record and not the one you use daily.
- Use a strong password that you have never used before and do not reuse it in other services.
- Change the access password to the portal or application if the company ever alerts of a security breach.
- If you need to save payment data, use a prepaid card provided by your bank.
- If the toy uses cloud storage, check that the website has an adequate level of encryption and change the default password.
See if it has reported any security issues:
We will investigate on the Internet if the smart toy we are going to buy has suffered security breaches before and if they have been solved. This will reveal to us whether the company cares about the privacy and safety of children.
Check that it has Security Settings:
Being an electronic device, the company should offer information on security measures. So we can know if it has a default password, if it receives updates, if it has parental control or if its ‘smart’ features can be completely shut down.
Configure your connected toy safely
A smart toy is not like your child’s other knick-knacks. Before connecting and playing with the device, we must open it with the child and explain what we are going to do next: configure it safely.
This is a great way to raise awareness among young people about the importance of keeping their data safe. By setting up the toy together, he can familiarize himself with the safety of the devices.
- Change the default credentials: this is the first security measure we must take when buying any device with a predefined password. In this way, we prevent cybercriminals from finding out easily.
- Check the privacy settings: If the toy has a configuration screen, go to it and disable the privacy features that the device does not need for it to work. If it uses an application, deny permissions in the phone settings and go to the app’s privacy settings as well.
- Check security settings: enable automatic security updates and other useful features to protect your family’s information.
- Disable features: if the settings allow it and you prefer that the toy not use the microphone, the camera, the location or the Internet connection, disable them in the settings.
- Check the data storage: if the toy stores information or a history of interactions, check them periodically and delete the stored data.
- Turn off the toy: if the device has a total shutdown mode, use it every time the child finishes playing. This will stop the data collection.
With these tips, playing with smart devices will be a safer activity for your children. And, if you need more information about connected toys, you can consult this Guide from the National Cybersecurity Institute (INCIBE) and its Safe Internet for Kids (IS4K) initiative.
